Cyber Security Products
BEL Cyber Security Products

Unidirectional Secure Gateway (USG)-Data diode
Data Diode provides a physically secure one-way communication channel from the one network to another network. In high security and critical infrastructure environments, to protect highly sensitive data and network, most commonly used security measure is to completely isolate the different networks. Security concern here is, usually USB drive or CD is used to transfer data from one network to another. USG solves these issues by creating a physically secure one-way communication channel from one network to another network. Key features of USG are unidirectional data transfer, higher performance, reliability and end-to-end security.
- Unique hardware-based, one-way communication at the physical layer
- Ensures data integrity
- Easy-to-use GUI (Graphical User Interface)
- Transfer of files
- Web-based solution
- Streaming of UDP data
- Folder synchronization

Hardware Security Module (HSM)
HSM is a secure memory device to generate and store vital data objects such as cryptographic Private/secret keys. It provides accelerated cryptographic operations such as encryption, digital signature, hashing etc. HSM provides function of key management. The Security aspects of Key Management are ensured and enhanced by the use of HSMs.

BES Token
BES Token provides digital certificate based multi-factor authentication in a token form factor enabling users to address PKI based security requirements. PKI tokens provide secure storage for digital certificates and private keys. They allow public-key cryptography and digital signatures to be leveraged securely, without risk of leaking the private key information. BES Token provides security for digital signature signing and verification.
Memory size: 64 KB (for storing digital certificates)
Password storage: Yes
Private key storage: Yes
USB interface: USB type A; supports USB 2.0
API & standards support: PKCS#11, PKCS#15 Compliant, MS CAPI, X.509 v3 certificate storage
Cryptographic Algorithm:
RSA-2048 Signature generation (On-board)
RSA-2048 verification (Off-board)
Hash Algorithm: SHA-1, SHA-224, SHA-256, SHA-512 (Off-board)
Random Number Generator: ANSI X9.31 PRNG or TRNG (passes NIST SP 800-22 test suite)
Certifications: As per CCA Guidelines
Supported OS: Windows (32 & 64 bit), Linux (32 & 64 bit)
Security: No method to extract, view, or access the private key
Temperature (Operating): 0°C to +50°C
Temperature (Storage): -50°C to +60°C
Casing: Hard moulded plastic, tamper-evident
Data retention period in memory: Minimum 5 years

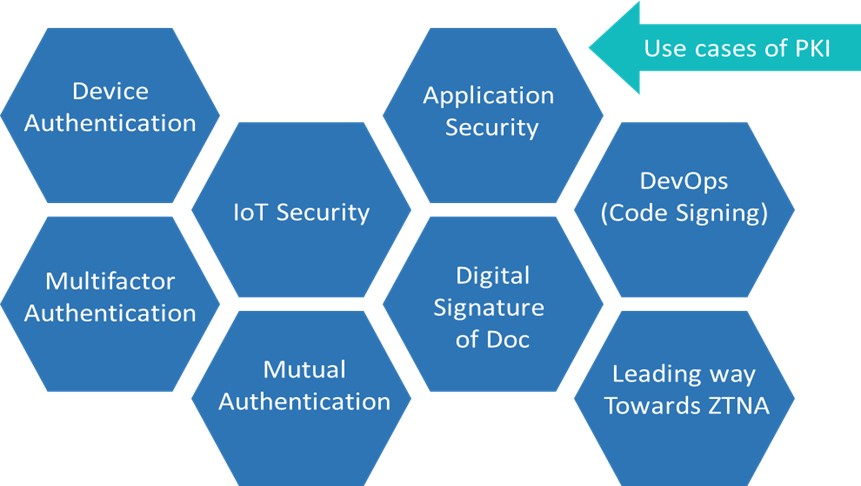
PKI (Public Key Infrastructure)
PKI solution provides complete Certificate life cycle management functionalities. PKI solution issues, renews, revokes and suspends digital certificates for its users and also maintains record of all transactions.Digital certificates can be used to secure transfer of information, assert identity information and verify authenticity of information.
Applications: Document signing, Secure email, Electronic commerce, Single Sign-On, Secure wireless LAN, Web services security, Web server security, Virtual private network and Code signing.

BEL Secure USB Flash Drive
It is designed to protect the important and critical data that is required to be transferred from one system to another. It prevents unauthorized access to the data present in the Flash Drive. The drive does not require any drivers or software to be installed. It’s a plug and play device. It can be used with any operating system.
- Allows user to authenticate before connecting to system
- PIN based Authentication via on- board keypad
- USB 2.0 HS interface
- Storage: 8GB/16GB/32GB/64GB
- AES-CBC 256-bit full disk hardware encryption
- Plug and play device
- No Operating system dependency

Network Encryptor
- It is high-speed standards based multi-protocol Encryptor specifically designed to secure data, voice and video information between trusted networks transmitted over an un-trusted network.
- AES-128/256 encryption
- Secure data transmission across Layers 2, 3
- End to end authenticated real-time network encryption
- Secure Key Management
- Built-in key server for the distribution of group keys
- Operates at data rates 10/ 100/1000Mbps for Ethernet and 1/10Gbps for Optical
- Supports both Ethernet and IP networks
- Tamper proof Hardware

Data in Transit Security (DiTS)
Data in Transit Security solution transparently captures & encrypts the unicast and multicast IP Packets based on packet filtering rules. The DiTS solution derives unique packet encryption key on-the-fly for each packet to do encryption/ decryption. This solution transparently encrypts the application data without session establishment and avoids forming of groups to multicast IP packets thus supporting Peer to Peer secure communication.
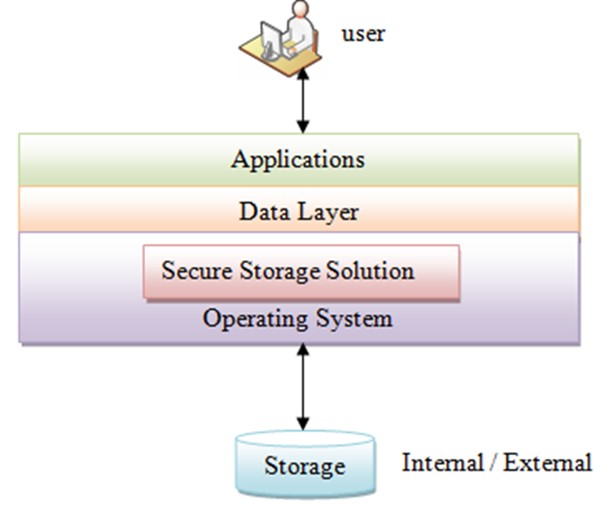
Data at Rest Security
The secure storage is a software solution that secures the data at rest for the DAS and SAN storages and protects the data during system maintenance and capture/theft. It provides encryption/decryption which is transparent to the user application.The data will be in encrypted form in the storage media. It has user friendly UI to view logs, health monitor, troubleshoot etc. Secure storage solution is available for both Windows and Linux platform.
System Integrity Solutions
System Integrity Management System (SIMS) is software-based solution which monitors the System Parameters and Applications and its associated configuration files for all the applications running in the Servers or work stations for their integrity.
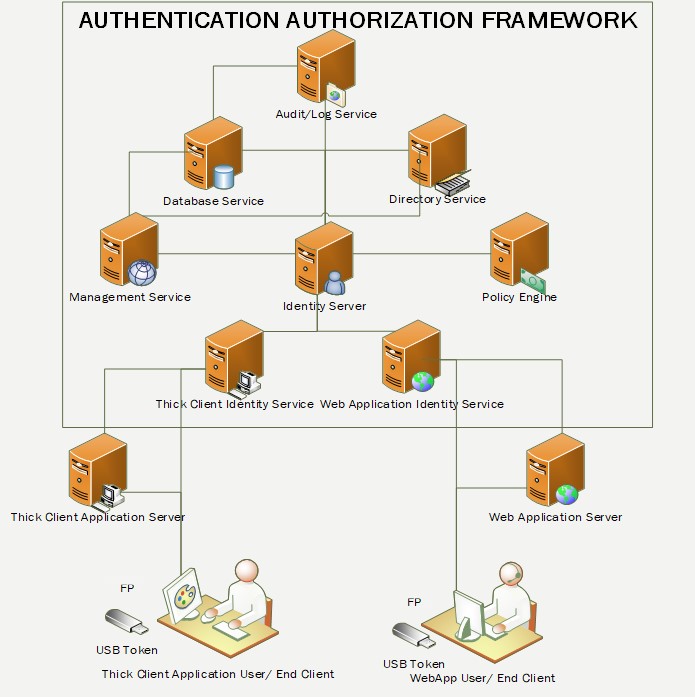
Authentication and Authorization Framework (AAF)
Authentication plays key role in tactical systems. Improper authentication and authorization mechanisms can cause a huge damage in tactical scenarios. Thus, tactical Systems require smart authentication mechanism and authorization. AAF is a generic framework to provide the Identity and Access Management irrespective of the application type, be it a web-based application or client server-based application or OS authentication.

Mail & Messaging solution
BEL has browser based interpersonal E-mailing solution that meets organizational need. BEL also has a Secure Formal Messaging solution is designed to suite messaging requirement of Defense environment and to provide Secure Messaging Solution to intelligence and government agencies. With this solution it is possible to achieve exchange of intelligence, operational and tactical data between users in a secure manner.

Android Vulnerability Scanner
AVS is vulnerability scanning tool for any applicationon the android device. AVS does static analysis for vulnerability scanning of the application’s disassembled code against published android CVE’s from NVD database and directed use cases for vulnerability detection including crypto issues, permission issues, X.509 certificate issues etc. Portable, modular and evolvable command line based tool.

